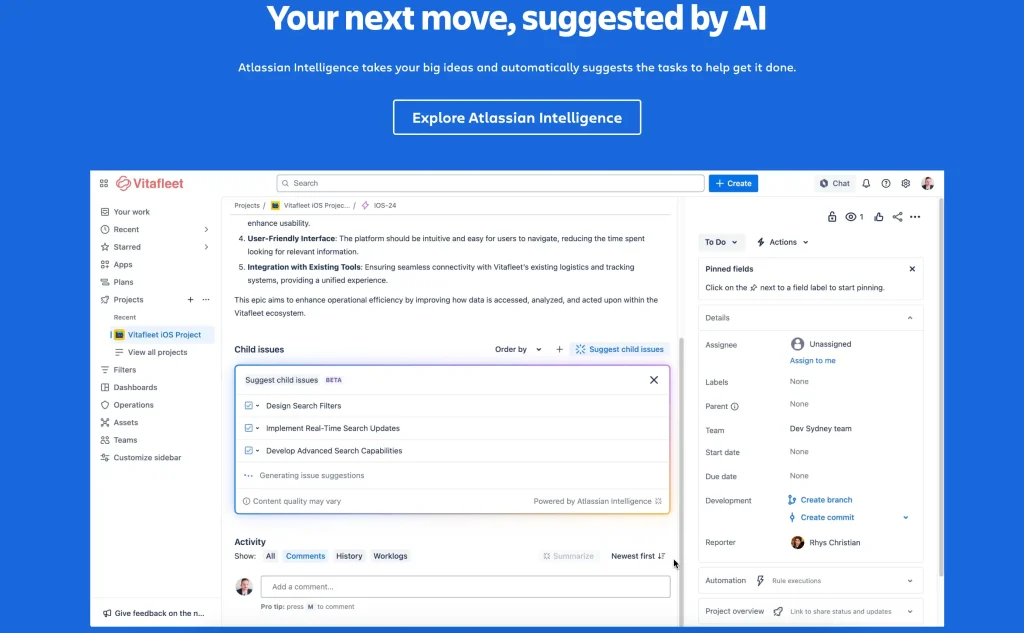
In today’s fast-paced digital world, many teams are moving to the cloud to boost collaboration, scalability, and overall efficiency. Atlassian products like Jira and Confluence have become key players in this shift, enabling seamless teamwork from virtually anywhere. However, as more companies embrace the cloud, a common concern arises: how secure is our data? This is where understanding cloud security and the concept of shared responsibility becomes essential.
In the cloud, security is a shared responsibility. It’s a collaborative effort between Atlassian and its customers to keep data safe, accessible, and compliant. Let’s dive into how this partnership works, what Atlassian takes care of, and what responsibilities fall on customers to ensure their cloud environment is fully protected.
Atlassian’s Responsibilities: Building a Secure Foundation
Atlassian takes on the foundational aspects of cloud security, from infrastructure upkeep to compliance, so customers can use their products with confidence. Here’s what Atlassian covers:
- Platform Security and Reliability
- Atlassian’s infrastructure is built to be resilient, with features like disaster recovery, high availability, and a 99.9% uptime service-level agreement (SLA). Their platform is designed to handle unexpected outages while supporting businesses and teams of all sizes. With failover mechanisms in place, Atlassian ensures that products like Jira and Confluence remain accessible, even during service disruptions.
- Infrastructure Maintenance
Atlassian maintains the physical infrastructure, including servers, networks, and data centers, that powers its cloud environment. They keep this infrastructure up-to-date with security patches and manage any hardware-related updates, so customers can focus on their own data without worrying about the underlying system.
- Compliance Certifications
Atlassian holds various compliance certifications such as ISO 27001, SOC 2, and GDPR. These certifications mean Atlassian’s systems are built and monitored to meet global standards for data handling and security. By adhering to these regulations, Atlassian provides customers, especially those in regulated industries, with a secure and compliant platform.
- System-Level Backups
Atlassian takes care of system-level backups to support disaster recovery efforts. These backups ensure that, if there’s a system-level problem, data can be restored and accessed again without issue. However, it’s important to note that while Atlassian provides platform-level backups, customers should still consider managing their own data backups, depending on their specific needs.
- Baseline Security for Marketplace Apps
Atlassian verifies the developers of Marketplace apps and scans them for vulnerabilities to provide a baseline level of security. By setting this standard, Atlassian allows customers to confidently integrate trusted third-party apps to extend their Jira or Confluence functionalities without compromising security.
Customer Responsibilities: Securing Your Environment
While Atlassian handles platform security, customers play an active role in managing their data and access controls. Here’s a breakdown of what customers need to focus on:
- User Access and Permissions
Customers are responsible for controlling who has access to their Atlassian environments. Setting up roles, reviewing permissions regularly, and ensuring that only necessary users have access to sensitive data is key to keeping information secure. For instance, if an employee leaves the company, their access should be promptly revoked to prevent any unauthorized access.
- Data Content and Management
Atlassian provides a secure platform, but customers control the data that gets stored within it. This includes organizing files, managing data accuracy, and deciding which information is appropriate to store in cloud-based systems. Sensitive data, such as personal information, should be stored with care and in accordance with relevant regulations and internal policies.
- Domain Verification
By verifying their domain, organizations can centrally manage all Atlassian accounts associated with that domain. Verified domains allow organizations to enforce authentication policies such as single sign-on (SSO) and multi-factor authentication (MFA), further enhancing their security by restricting access to authorized users only.
- Marketplace App Selection
While Atlassian provides baseline security for Marketplace apps, customers should carefully assess apps before installing them. Reviewing permissions requested by the app and verifying that they align with your organization’s policies can help avoid unnecessary risks. For example, only allow apps that meet internal standards and provide necessary functionalities without overextending permissions.
- Password Policies and Authentication
Implementing robust password policies is a must. With Atlassian Access, customers can enforce SSO, MFA, and other security measures for stronger user authentication. Enforcing periodic password changes and encouraging users to create complex passwords helps minimize the risk of unauthorized access.
Real-World Examples of Shared Responsibility
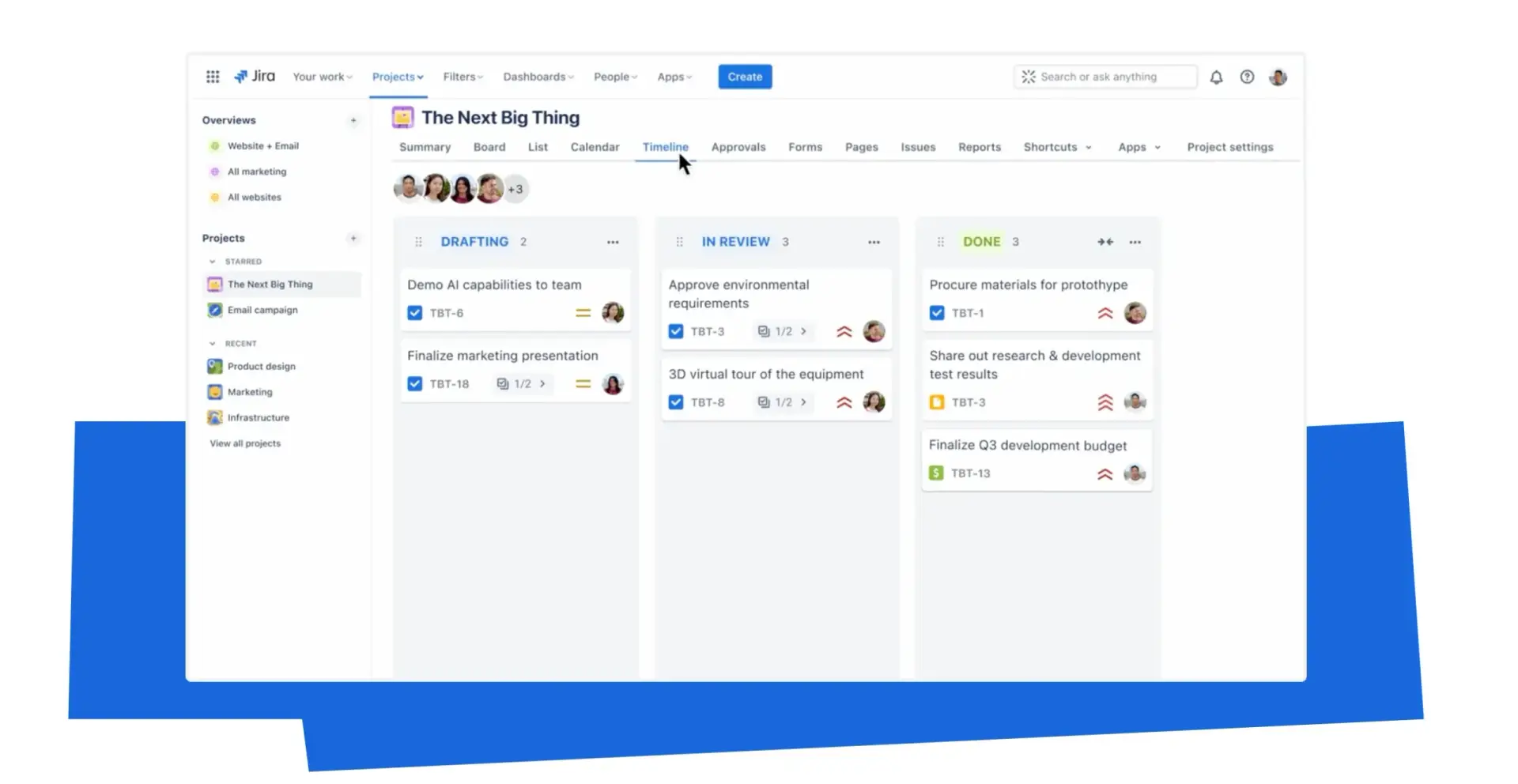
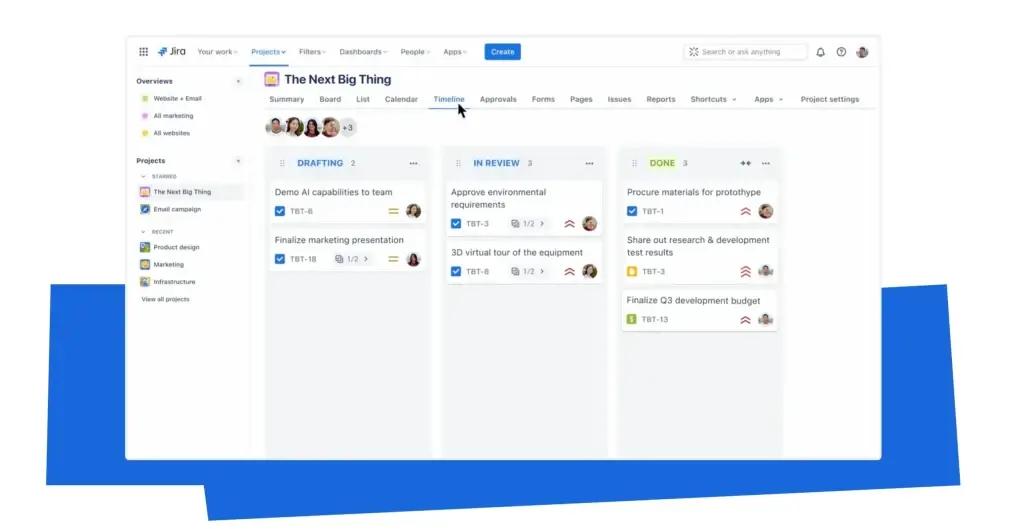
Imagine a company using Jira for project management. Atlassian’s platform ensures uptime, data protection, and a range of compliance measures, but the IT team at this company must still monitor access permissions. They verify their domain, set up centralized access, and enable MFA for added security. Additionally, they select only trusted Marketplace apps that meet their security requirements, helping to keep their environment secure.
Practical Tips for Customers
To make the most of this shared security model, here are some practical steps you can take:
- Regular Access Reviews: Schedule quarterly reviews of user access to ensure that only those who need access have it. This practice reduces security risks by promptly identifying and removing unnecessary access.
- Use Atlassian Access for SSO and MFA: Atlassian Access offers centralized management tools for authentication, making it easier to enforce strong password and MFA policies across your organization.
- Audit Marketplace Apps: Regularly review the apps you’ve installed from the Marketplace. If an app’s permissions no longer align with your security standards, it might be time to consider alternatives.
- Create a Data Management Policy: Decide what types of data are appropriate for storage in Atlassian products. This helps users understand data guidelines and prevents unnecessary risks related to sensitive information storage.
Actionable Steps for Strengthening Your Security
- Verify Your Domain: Verify your organization’s domain to take full control of user management, enforce SSO, and strengthen overall access control.
- Enable Two-Factor Authentication (2FA): 2FA is a simple but highly effective way to add an extra layer of protection, making unauthorized access much harder.
- Train Your Team on Security Best Practices: Security is most effective when everyone is on board. Encourage users to create strong passwords, avoid suspicious links, and report unusual activities.
- Monitor Compliance Updates: Atlassian’s Trust Center provides updates on compliance changes and new certifications. Keeping an eye on these updates helps ensure your organization stays compliant and informed.
Conclusion: A Strong Partnership for Secure Cloud Usage
Cloud security is a collaborative effort. Atlassian provides a secure, resilient platform, but customers need to actively manage their data and user controls. By understanding and fulfilling your responsibilities, you can build a stronger, more secure partnership with Atlassian, ensuring that your data is protected and your organization remains compliant. Together, you and Atlassian make cloud security work.